Prevent Lateral Threat Movement,
Without the PAIN of Manual Segmentation
Prevent Lateral Threat Movement,
Without the PAIN of Traditional Segmentation
Automate Everything:
Device Discovery to Zero Trust Micro-Segmentation in Minutes, with 1 Click!
Trusted by









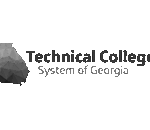
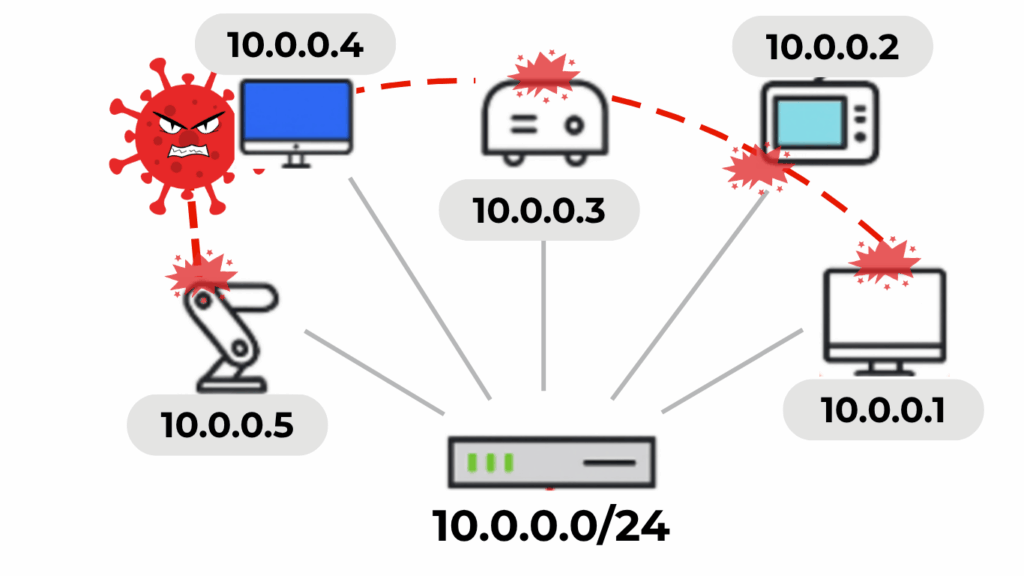
Traditional segmentation leaves gaps.
Traditional segmentation like VLANs can help to limit the attack surface, but it drains resources and is susceptible to unhindered lateral threat movement within the VLAN, as well as into the main network due to generic policies and policy drift—putting your entire network in danger.
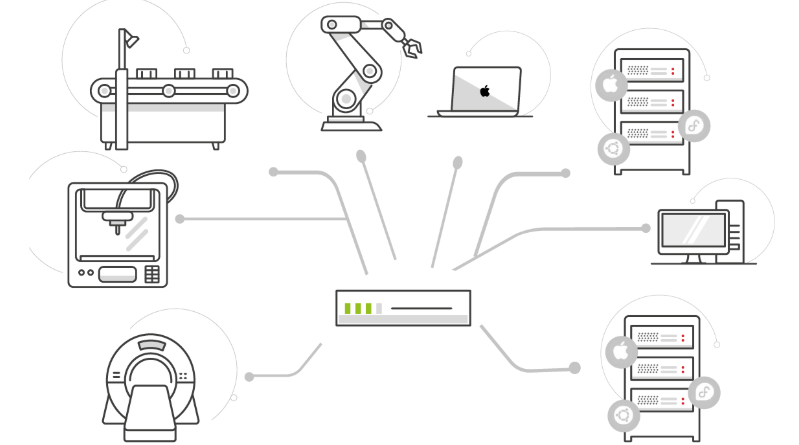
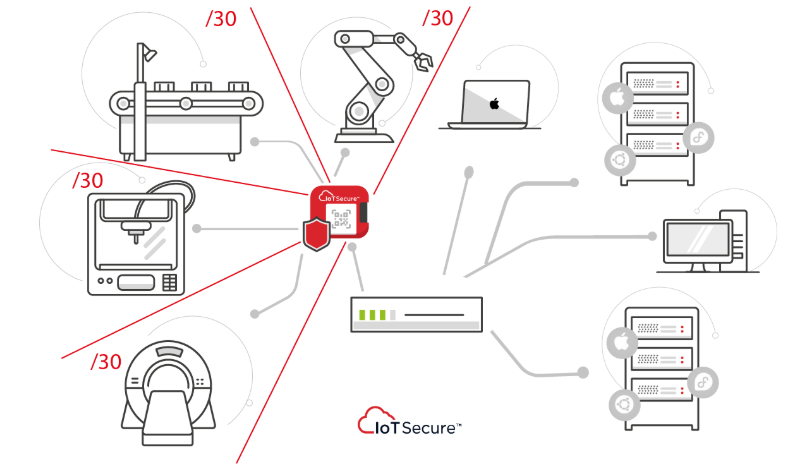
Micro-segmentation fixes the gaps, but there’s a problem:
It’s too much work to scale on unmanaged/xIoT devices
But Not Anymore!
IoTSecure makes micro-segmentation effortless with advanced automation.
Shared VLANs:
-Limited protection
-Significant work
-Never-ending maintenance
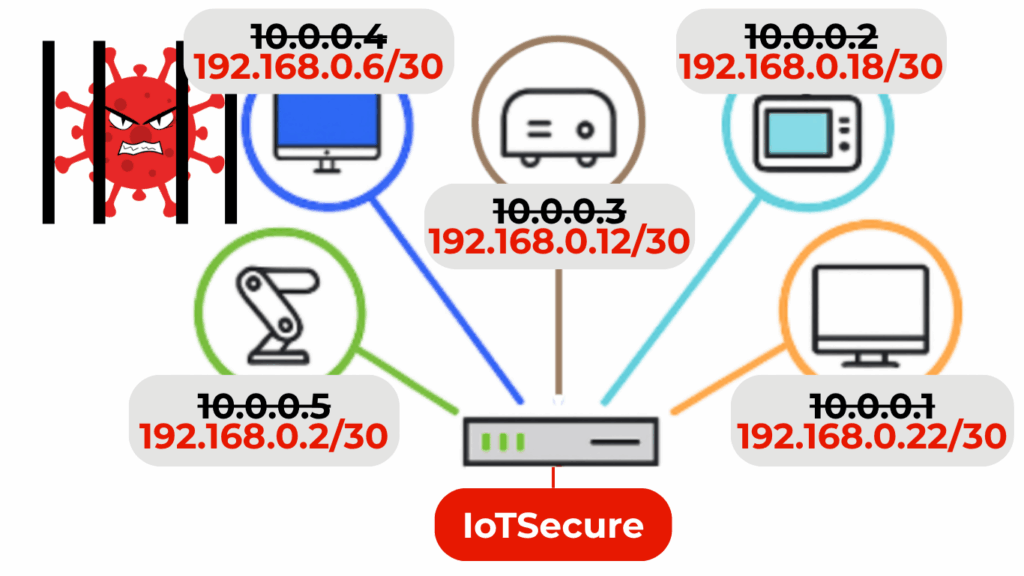
IoTSecure:
-Advanced protection
-Almost zero work
-Dynamic maintenance
Traditional segmentation means extensive manual work
Step 1: Discover & Identify xIoT devices
Step 2: Capture device traffic and user access
Step 3: Analyze device and user traffic patterns
Step 4: Potentially upgrade infrastructure
Step 5: Create network segments
Step 6: Create and implement security policies
Step 7: Endless policy maintenance

Endless manual work to create and maintain device inventories, VLANs and policies, and infrastructure upgrades.

Deploy in Minutes – 1 Click and Done!
Complete automation from device discovery to ZeroTrust micro-segmentation, without any infrastructure upgrades or tuning.
Who Has Time?

Security zone definitions that take weeks to define
Incomplete device discovery & identification & policy drift
Mapping traffic flows and whitelists/blacklists across evolving networks

Policy creation and endless maintenance
Prevent Lateral Threat Movement Before it Starts
For a Fraction of the Time and Cost vs. Traditional Segmentation
Our patent-pending platform replaces tedious, repetitive manual work with intelligent automation – from device discovery to Zero Trust micro-segmentation, and everything in between, with a single click.
Steps
Automation
Discover & Identify xIoT
Capture device traffic
Analyze device traffic
Create segments
Create / deploy policies
Policy maintenance
Deployment Time
Traditional
Weeks +
IoTSecure
< 1 Hour
3 form factors for any use case





3 form factors to choose from to best meet your use case

Connect to any standard port, and set the appliance as the DHCP server. Your existing DHCP server is automatically used for failover.

Automate device discovery, micro-segmentation policy generation …and everything in between.

Deploy, dynamically monitor and refine policies with a single click. Protect the network from xIoT & protect xIoT from each other.